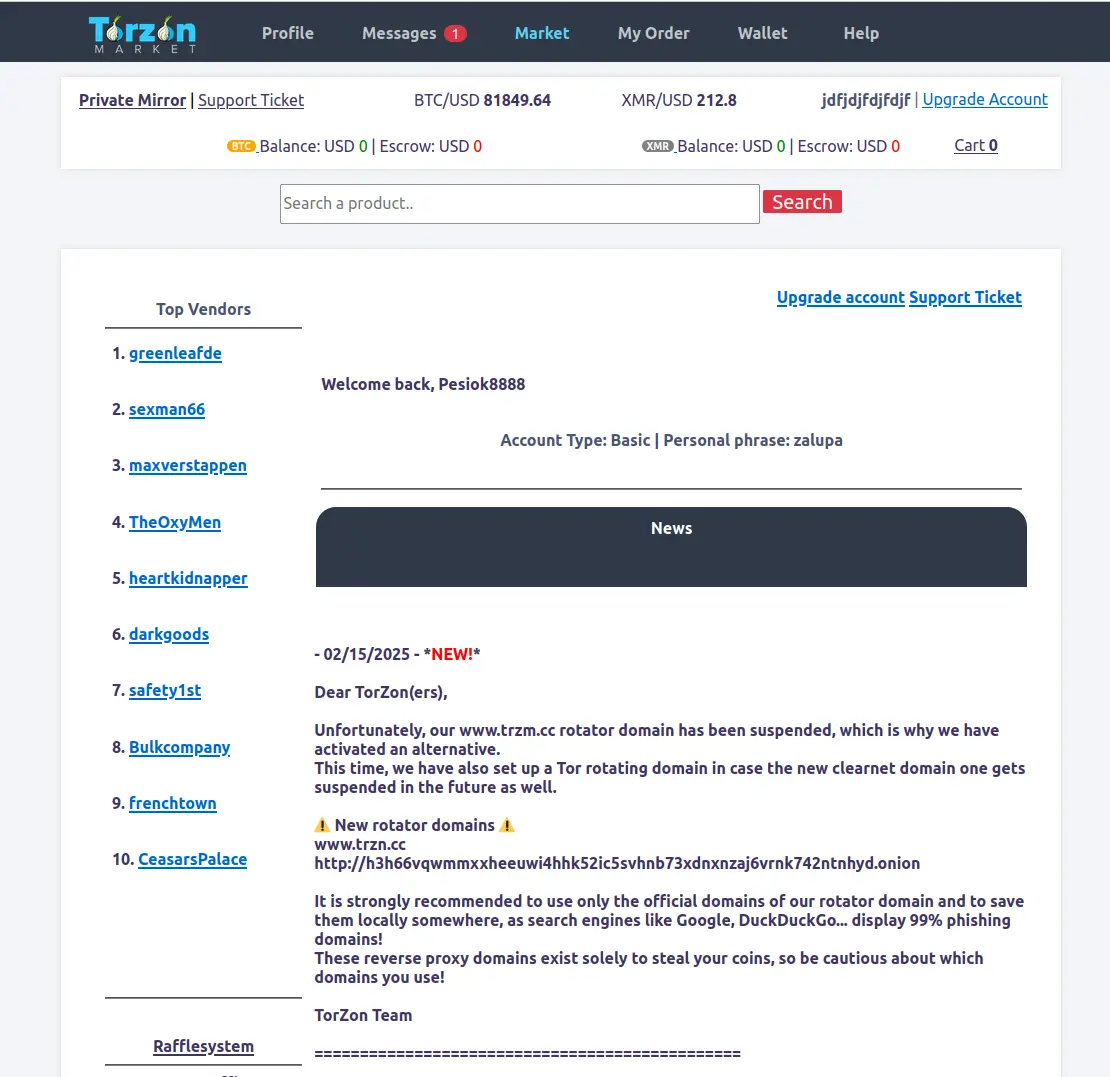
TorZon Market Links List
Official verified onion links for secure access
Verified Onion Mirrors
Always use these official mirrors for secure access
Bookmark this page for the latest access links. Only use these verified mirrors for your safety.
How to Connect Securely
Key steps to maintain anonymous and protected access
Install the Tor Browser
Download and install the official Tor Browser from the Tor Project. This browser encrypts and routes your traffic through multiple anonymous relays, protecting your identity and activity. Avoid using standard browsers, as they do not support onion services or provide the necessary privacy safeguards.
Use a Trusted VPN
Before launching Tor, connect to a reputable VPN that does not keep logs and supports crypto payments. A VPN hides your real IP address from your ISP and adds an extra layer of privacy before your traffic even reaches the Tor network.
Run Tails OS (Optional)
For advanced users seeking top-tier anonymity, consider using Tails — a secure, live operating system that runs from a USB stick. It leaves no trace on your device and forces all internet activity through the Tor network, making it ideal for accessing darknet platforms securely.
Security Visualization

Frequently Asked Questions
Answers to common concerns about accessing TorZon Market
If a mirror appears offline, try one of the other verified mirrors listed on this page. Downtime can occur due to server maintenance or network instability. Always rely on the official mirror list to maintain safe and uninterrupted access. Avoid using unverified links from third-party sources.
To stay secure, always browse using the Tor Browser with the highest security level enabled. Use a trusted VPN before launching Tor, disable JavaScript, and avoid downloading files. Keep your system updated and consider running Tails OS for complete anonymity. Never reveal personal details or use real-world identities.
Access to this site is provided solely for informational and educational purposes. Users are fully responsible for adhering to the laws of their respective jurisdictions. TorZon Market does not enable or endorse any illegal activities. Proceed at your own risk and always consult legal counsel if unsure.
Link Verification System
How we keep you safe from phishing attacks
PGP Verification
Every mirror link is cryptographically verified using official Torzon PGP signatures
Real-Time Monitoring
Automated systems check uptime, SSL certificates, and authentication 24/7
Blacklist Protection
Known phishing sites are blocked and reported to protect the community
Load Balancing
Multiple mirrors maintain 99.7% uptime even during DDoS attacks
Quick Access Guide
3 steps to secure Torzon access
Install Tor Browser
Download from torproject.org only. Set security to "Safest" level.
Choose a Mirror
Copy any verified onion link from the list above. Use Primary mirror for best performance.
Verify & Access
Check the full .onion address character-by-character before logging in.
Security Best Practices
Always Do
- Bookmark torzon-darknet.ink
- Use VPN + Tor Browser
- Verify full onion addresses
- Check for "Primary" badge
- Enable 2FA on your account
Never Do
- Trust links from forums/messages
- Use regular browsers
- Enable JavaScript
- Save passwords in browser
- Access without VPN
Mirror System Explained
Why Multiple Mirrors?
Each mirror is a synchronized copy of Torzon Market, ensuring continuous access during DDoS attacks or server maintenance. All mirrors share the same database and accounts.
Primary Mirror Badge
The "Primary" mirror is the original, longest-running address. While all mirrors are identical, the primary may receive updates slightly earlier. Use any verified mirror with confidence.
Security Rotation
Mirrors are regularly rotated to prevent long-term traffic monitoring. Always check this page for the latest verified onion addresses.
Cryptocurrency Wallet Security for Torzon Market
Protect your Bitcoin and Monero when using Torzon darknet marketplace
Critical Security Rules for Torzon Market Transactions
Secure Payment Workflow for Torzon Market 2025
Purchase BTC/XMR from exchange using anonymous payment methods (cash vouchers, crypto ATMs)
Transfer to Electrum (BTC) or Monero GUI (XMR) on your device. Use VPN + Tor during withdrawal.
Use Wasabi Wallet CoinJoin or mixing services to break transaction history before Torzon Market
Visit torzon-darknet.ink → Copy official onion link → Verify full address character-by-character
Send from your personal wallet to Torzon deposit address. Use custom fees for optimal confirmation time.
Advanced Privacy Tips for Torzon Marketplace
🔥 Maximum Anonymity Setup
- Use Tails OS with persistent Electrum/Monero wallet
- Access Torzon only through Tor Browser (never clearnet)
- Generate new wallet addresses for every Torzon transaction
- Wait 6+ confirmations before considering BTC deposits final
- For XMR, 10 confirmations provide full privacy on Torzon Market
Speed vs Privacy Balance
- Fast but traceable: Bitcoin with high fees (30 min)
- Balanced: Bitcoin through mixing (2-4 hours)
- Maximum privacy: Monero direct to Torzon (20-30 min)
- Best choice for Torzon Market: XMR via Monero GUI wallet over Tor
Torzon Phishing Detection & Prevention
How to identify fake Torzon clones and avoid scams
WARNING: Phishing Epidemic on Darknet Markets
Phishing sites are the #1 threat to Torzon Market users. Scammers create fake clones that look identical to the real marketplace but steal login credentials and cryptocurrency deposits. An estimated 200+ fake "Torzon" sites operate at any time, appearing in forum posts, private messages, and even search results.
CRITICAL RULE: Only trust onion mirrors listed on torzon-darknet.ink. Bookmark this page immediately. Never access Torzon through links from messages, forums, or search engines — 95% are phishing attempts.
Red Flags of Phishing Sites
- ✗ Different URL: Onion address doesn't match verified list on this page
- ✗ No PGP Signature: Missing official Torzon PGP-signed welcome message
- ✗ Urgent Warnings: "Account suspended" or "Verify wallet" messages immediately after login
- ✗ Deposit Requests: Asks you to send Bitcoin to "activate account" or "unlock features"
- ✗ Typos/Poor Grammar: Professional Torzon has zero spelling errors in interface
- ✗ SSL Certificate Errors: Browser shows security warnings about invalid certificates
Legitimate Torzon Indicators
- ✓ Verified URL: Exact match with onion addresses listed on torzon-darknet.ink
- ✓ PGP Signed: Footer contains verifiable PGP signature from official Torzon key
- ✓ Consistent Branding: Logo, colors, and layout match known screenshots
- ✓ No Urgent Demands: Real Torzon never pressures immediate deposits or actions
- ✓ Professional Quality: Zero typos, consistent terminology, polished interface
- ✓ Valid SSL: No browser security warnings or certificate errors
🔍 Step-by-Step Verification Process
Visit This Page
Always start at torzon-darknet.ink — never search engines
Copy Verified Mirror
Use copy button — don't type manually to avoid errors
Verify Full Address
Check all 56 characters match — scammers change 1-2 letters
Check PGP Signature
Scroll to footer — verify PGP signed message is present
💀 If You Entered Credentials on a Phishing Site
Immediate action required — your account and funds are at risk
Immediate Steps (5 minutes)
- Access real Torzon from verified mirror on this page
- Change password immediately using current credentials
- Enable 2FA if not already activated
- Change PGP key to new key pair
Security Measures (1 hour)
- Withdraw all funds from Torzon wallet to personal wallet
- Generate new cryptocurrency addresses
- Review recent orders for unauthorized activity
- Contact vendors about potential account compromise
⏰ Act within 15 minutes — phishing operators work fast to drain wallets
How Tor Network Protects Torzon Users
Understanding the technology behind anonymous marketplace access
What is Tor and Why Torzon Requires It
Tor (The Onion Router) is free open-source software enabling anonymous internet communication. Unlike regular browsing where your ISP and websites see your real IP address, Tor routes traffic through three random encrypted relays before reaching Torzon Market. Each relay only knows the previous and next hop — no single node knows both your identity and destination.
Torzon operates exclusively as a .onion hidden service accessible only through Tor Browser. This architecture means Torzon servers don't know user IP addresses, and ISPs cannot determine which websites Tor users visit. The combination of Tor network and .onion hosting provides double-layered anonymity protecting both Torzon marketplace and its users from surveillance.
Entry Node (Guard)
Your Tor Browser connects to an entry node that sees your real IP address but not your Torzon destination. Entry nodes know you use Tor but cannot determine you're accessing Torzon Market. Your ISP sees encrypted Tor traffic to entry node but no further visibility.
Middle Relay
Middle relay knows entry node and exit node but not your IP or Torzon destination. This relay adds additional encryption layer and routing obfuscation. Middle relays change every 10 minutes, making long-term traffic correlation attacks against Torzon users extremely difficult.
Exit Node
Exit node connects to Torzon .onion service but doesn't know your identity. For hidden services like Torzon marketplace, traffic never actually exits Tor network — connection remains encrypted end-to-end. This architecture means accessing Torzon provides stronger anonymity than regular websites.
Tor Security Limitations & Best Practices
✓ What Tor Protects
- • Your IP address from Torzon Market
- • Your browsing from ISP surveillance
- • Traffic content from network monitoring
- • Location from Torzon administrators
What Tor Doesn't Protect
- • Poor OPSEC (mixing identities)
- • Malware on your computer
- • Social engineering attacks
- • Physical package interception